Redirection is an HTTP response type that informs clients that they are being sent to a different page. When a browser receives this response, it loads the URL defined in the page’s Location header, sending the visitors of one domain to the new destination URL. While redirection and forwarding are essential in directing users across pages, security gaps may allow attackers to force users to unwanted sites. This article discusses unvalidated redirects and forwards vulnerability, its impact, and various remediation practices.
Don’t have time to read? Listen to this blog post instead.
What Are Unvalidated Redirects and Forwards?
If a web application is susceptible to the URL redirection vulnerability, it accepts untrusted URL inputs that may cause it to redirect an innocent user’s request to malicious sites. Adversaries can craft a malicious URL within the untrusted input, redirecting victims to the attacker’s fabricated site where the user fills a login form with their credentials. This vulnerability, also known as Open Redirects, allows hackers to create links that bypass the web application’s security checks to escalate their privileges and perform privileged functions.
The redirection vulnerability does not directly affect web applications, as it lets hackers lead users to malware sites. Websites susceptible to open redirect attacks are mainly used to orchestrate phishing scams and other social engineering attacks, which harm the website’s reputation. The open redirect vulnerability continues to be one of the top OWASP vulnerabilities that can be exploited to orchestrate chained attacks in web applications and their underlying systems.
Impact of Unvalidated Redirects and Forwards
Unvalidated redirect and forward attacks are not as prevalent since they need to be part of a chain attack or precede a phishing attack. However, since the open redirect vulnerability is easy to exploit, attackers are highly motivated to detect and abuse it. Furthermore, a successful open redirect attack opens the application to various other forms of attacks, including:
1. Cross-site scripting attacks where the web application uses browser-accepted data or Javascript protocols in the redirects
2. Bypassing Content-Security-Policies if whitelisted domains are susceptible to open redirects
3. Evading server-side request forgery (SSRF) filters
4. Response headset splitting/Carriage Return and Line Feed (CRLF) attacks
Depending on the user accounts that have been compromised and the magnitude of the chain attack, impacts of an unvalidated redirect attack range from mild to severe.
How to Prevent Unvalidated Redirects and Forwards?
There are multiple ways to prevent open redirect vulnerabilities, including:
Using Safe URL Redirects
Developers can adopt coding best practices to automatically route requests to a different page without having to perform some action. In addition, since developers explicitly declare the new URL in the code, attackers cannot manipulate and perform unsafe redirects.
A safe redirection function can be implemented for most development frameworks. Examples include:
1. Java – response.sendRedirect(“http://www.darwin.com”)
2. ASP.NET – Response.Redirect(“~/folder/Login.aspx”)
3. Rails – redirect_to login_path
4. PHP – header(‘Llocation: ‘.$redirect_target.php);
Avoid Redirects
URL redirection serves almost no purpose and should be avoided whenever possible. Besides being a cyber-attack vector, multiple redirects in a website also introduce an overhead, significantly slowing down the application’s response time. Therefore, it is recommended that developers only implement redirects when changing the location of a page/site without substantially impacting the user experience.
Enable Additional Protection for the URL parameter
Developers should ensure the web application does not accept URLs as the user’s input for destination parameters. Instead, if necessary, the client should be asked to provide an ID, token, or response code mapped to a target on the server-side. This technique protects the application from adversaries that inject malicious URLs redirecting victims to untrusted sites with a trustworthy appearance.
Exclude Search Engines from Redirect Scripts
Developers should include a robots.txt file listing search engine crawlers. This keeps manipulators from tricking users into clicking malicious links via web search results.
Validate Safe URLs
When redirecting requests to external URLs, developers should use IP filtering and other server-side request forgery prevention techniques that enable the application to determine whether the target URL is safe or not.
Whitelist Trusted URLs
Sanitize URL user input by listing trusted URLs in a regex or hosts file. The whitelist (allow-list) is more effective than the blacklist as it allows for stricter control of target URLs in user-supplied input forms.
Notify Users of the Redirect
It is a recommended best practice to force the redirect into a notification page informing the user when they are being redirected. This page should also include the target URL, with a link the users should click to confirm that it is a trusted destination.
Remediation of Unvalidated Redirects and Forwards
There are several measures that organizations can leverage to remediate redirection vulnerabilities. These include:
Eliminating Redirection Functions
Replacing redirection functions in the application with direct links to the redirect target minimizes the chances of success for phishing attempts.
Use Relative URLs for Redirect Links
This automatically implements the same-origin policy, enforcing appropriate validation by ensuring all redirects come from the same web server that sends the HTTP response.
Enforce Internal Redirects
Major programming languages include a local redirect helper method that throws an exception if the request is redirected to a non-local URL. This implements a minimum filtering policy that restricts redirects to a local subdomain.
How Crashtest Security Can Help You With Unvalidated Redirects and Forwards
The Crashtest Security Suite helps organizations harden their JavaScript, APIs, and web applications against security risks by establishing a continuous testing mechanism. The suite includes an automated vulnerability scanner that benchmarks the web application against OWASP risks, such as unvalidated redirects and forwards.
Crashtest Security’s comprehensive penetration testing identifies chain attack patterns by automatically exploiting and reporting on uncovered attack surfaces. Start your free, 2-week trial to know how you can reduce the risk of being hacked through an input validation flaw.
This article has already been published on https://crashtest-security.com/unvalidated-redirects-forwards/ and has been authorized by Crashtest Security for a republish.
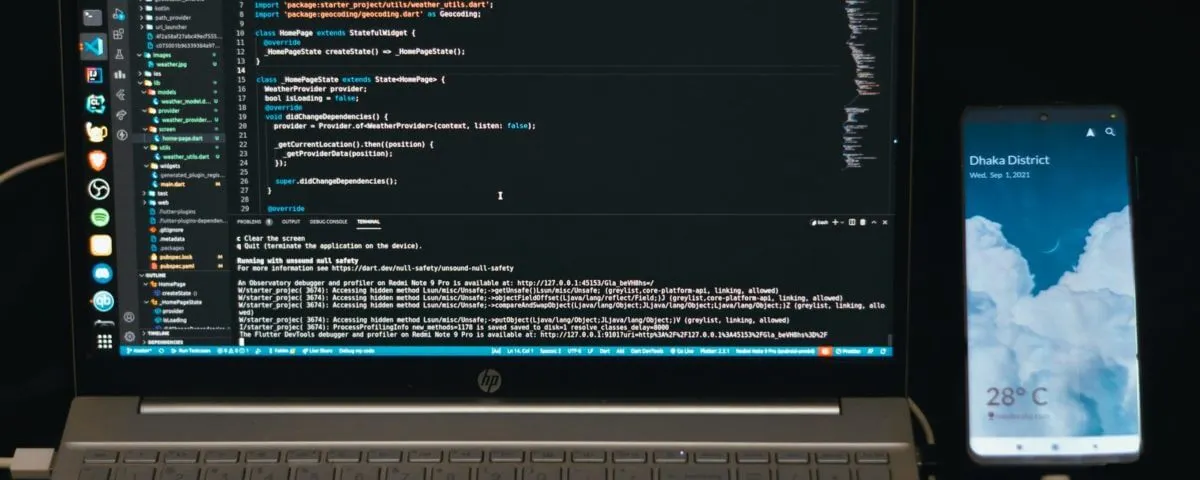
Featured Image Courtesy – Photo by Fahim Muntashir on Unsplash